3 months to 30 minutes
Security design reviews that keep up with modern development
SecurityReview.ai analyzes docs, diagrams, code, and engineering tickets to identify risks and generate compliance-ready threat models.
Run continuous security reviews without the never ending back & forth between security and dev team for product info and getting into scheduling nightmares.

Threat Modeling and Security
Design Reviews are now required by
modern security frameworks

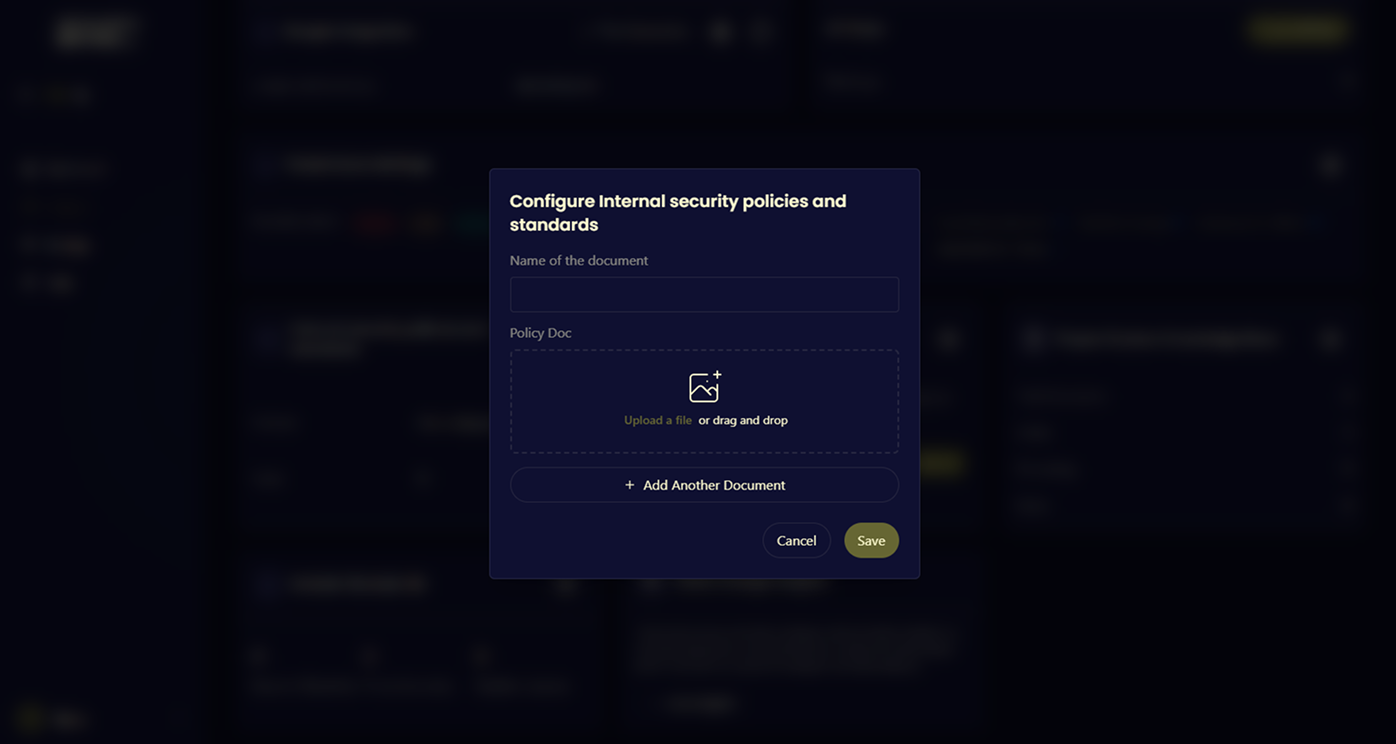
Frameworks like PCI DSS, ISO 27001, and the EU Cyber Resilience Act require formal threat modeling as part of secure system design. SecurityReview.ai generates architecture-based threat models and mapped controls automatically, so teams meet compliance requirements without slowing engineering.
Security teams gain continuous risk visibility.
Auditors get provable controls.
Stop choosing between engineering velocity and regulatory readiness. Get both.
Security reviews weren’t built for
modern development
Manual threat modeling
Security teams spend weeks collecting documentation, recreating architecture context, and preparing for review sessions before analysis even begins.
Expert bottlenecks
Most organizations rely on a few security architects to run threat modeling and design reviews across dozens of engineering teams.
Limited security bandwidth
Security teams rarely scale at the same pace as development. As systems multiply, review coverage shrinks.
Stale threat models
By the time the review finishes, the architecture has already changed.
A better way to run security design reviews
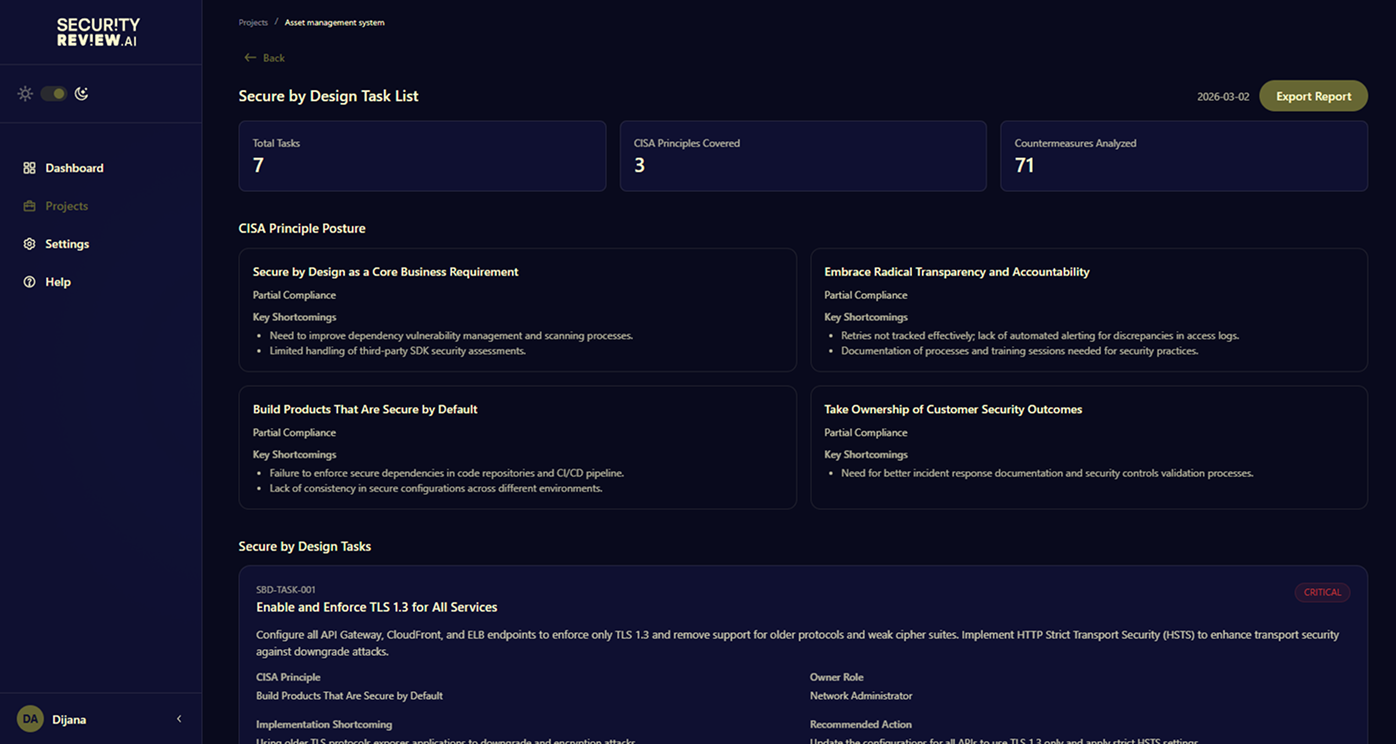
01. Continuous design-stage security
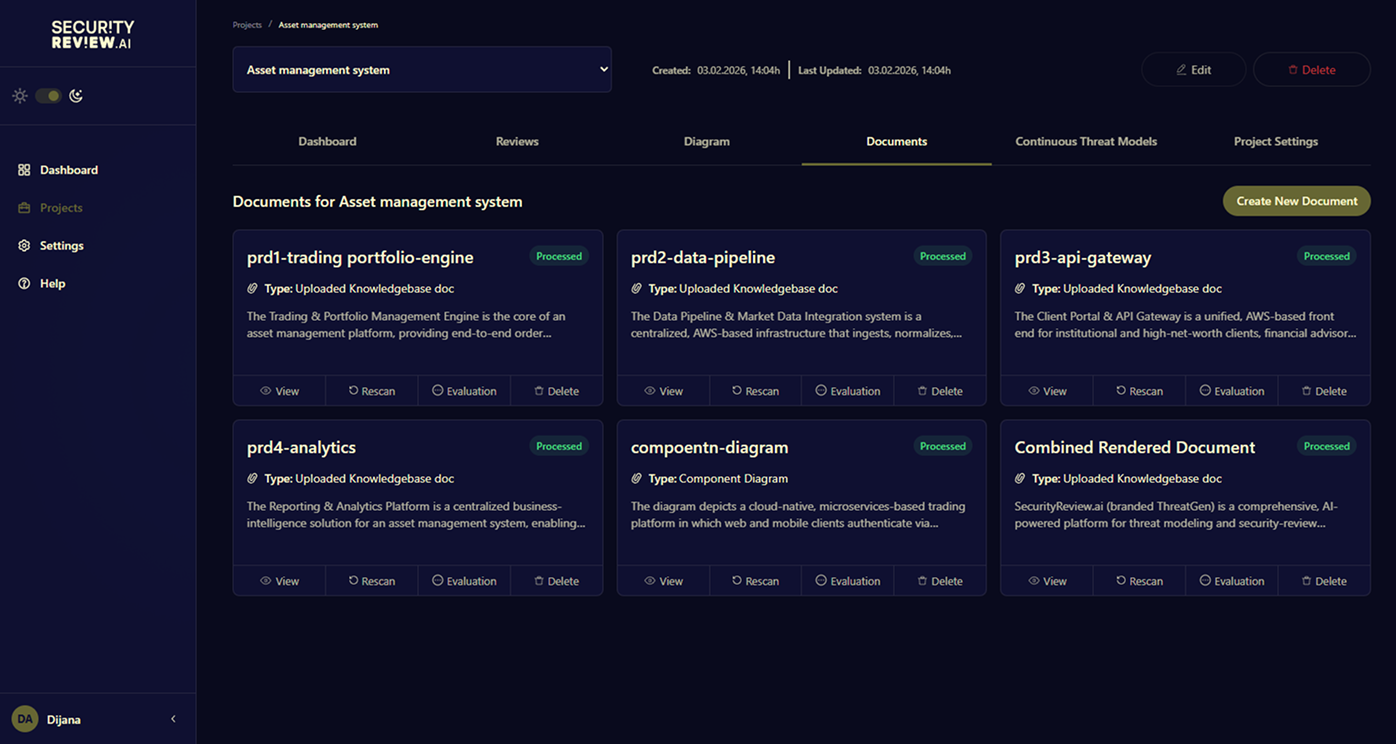
SecurityReview.ai analyzes your architecture and documentation to detect security risks before code reaches production.
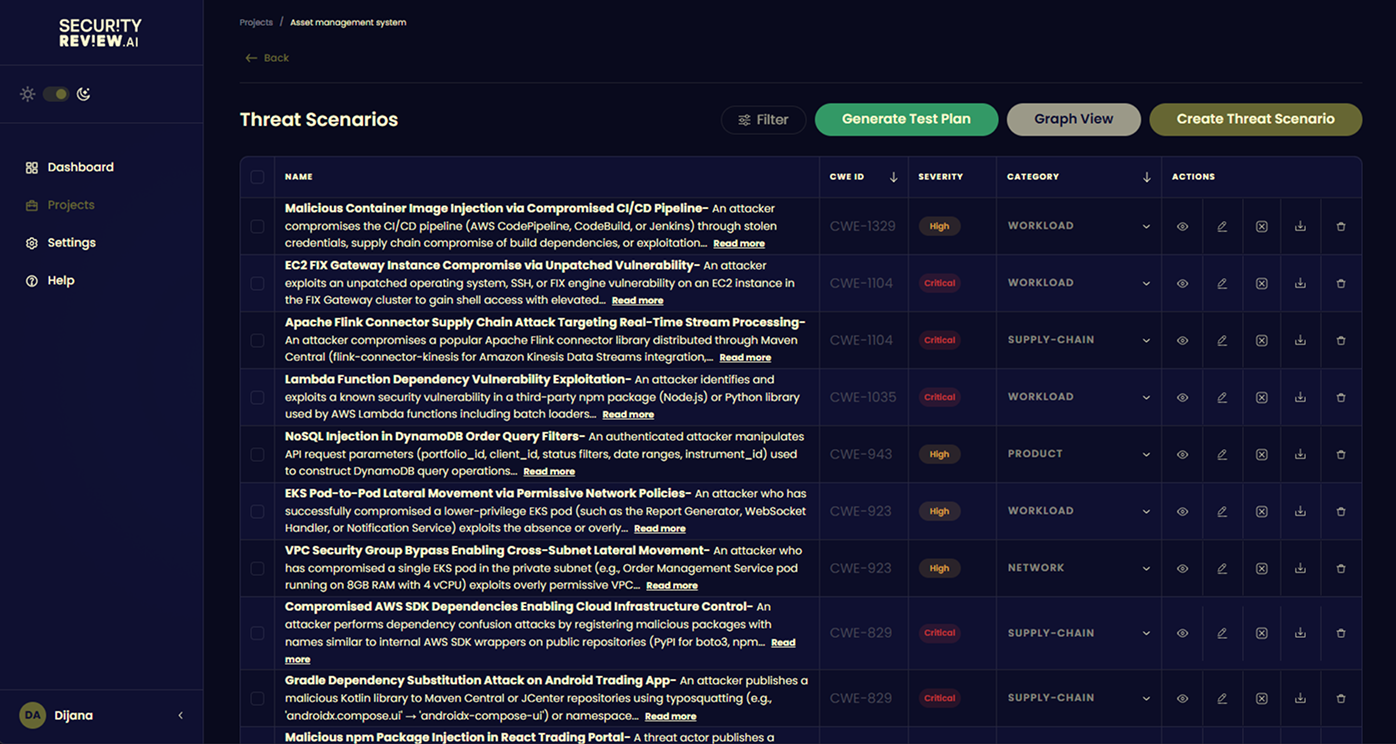
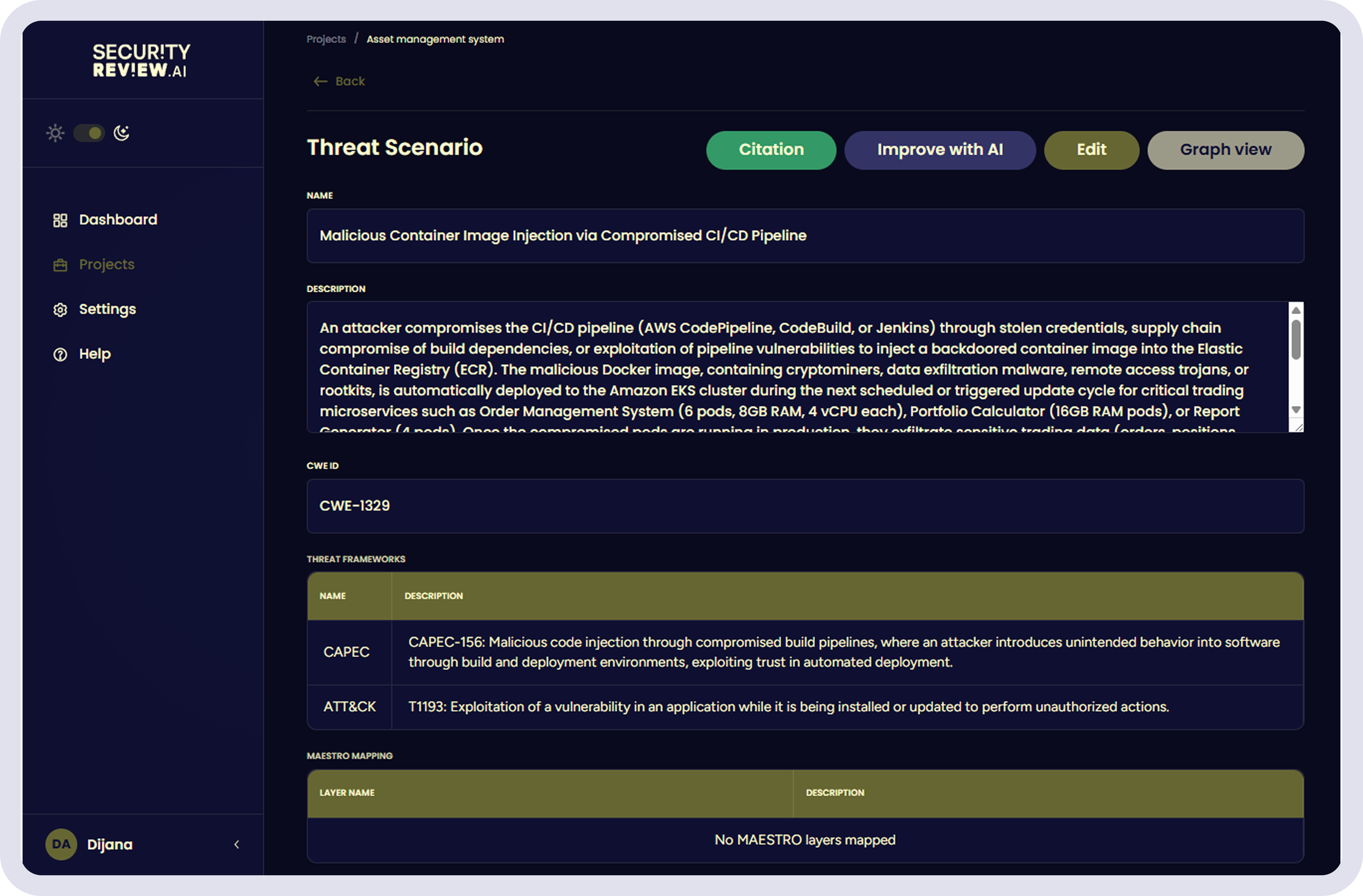
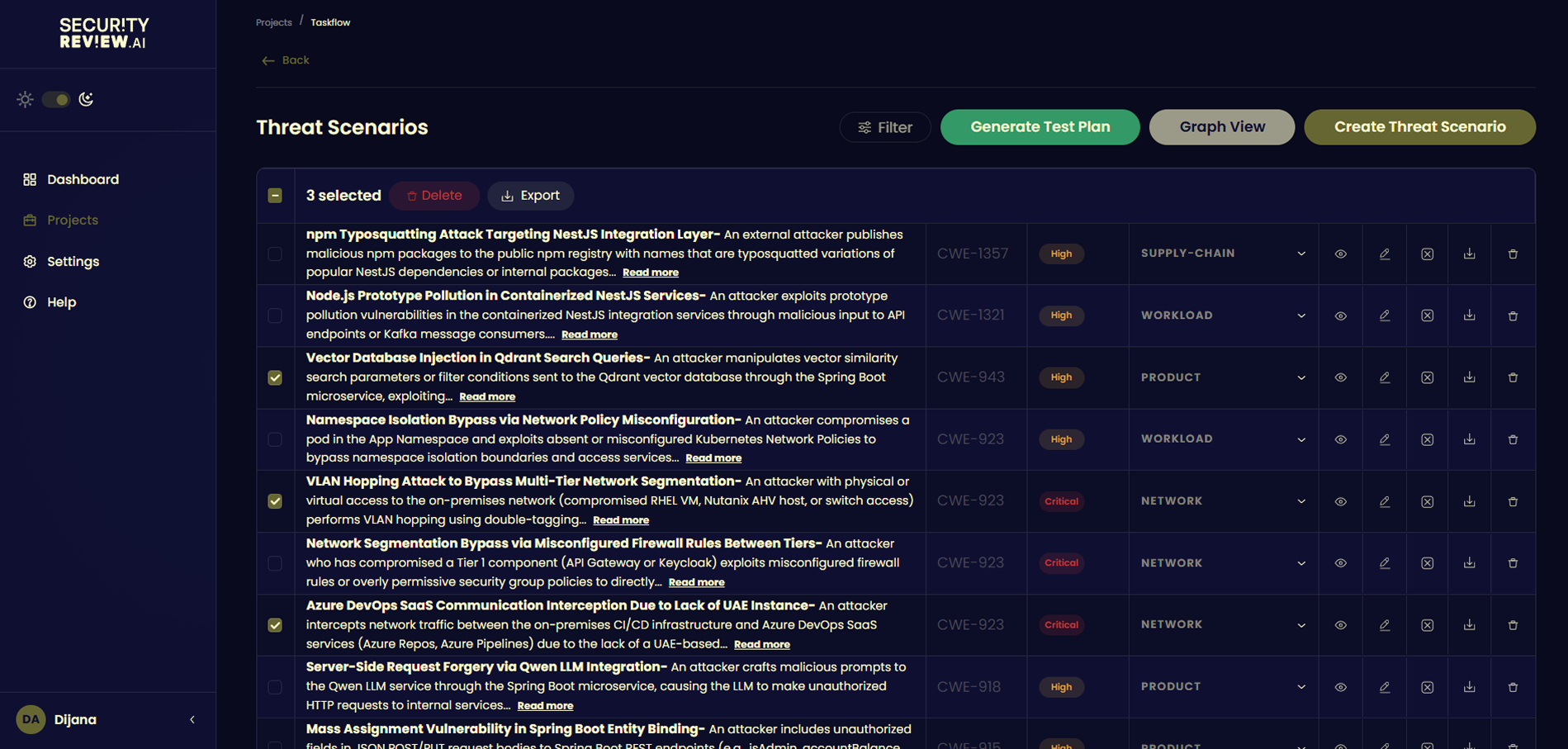
02. System-specific threat modeling
Threats are generated based on your actual services, data flows, and integrations instead of generic checklists.
03. Security that scales with development
Run consistent security reviews across systems without relying on workshops or scarce security architects.

Confluence
Jira
GitHub

Google Docs
Slack

ServiceNow
Architecture diagrams
Product specs
Design discussions
Engineering tickets
Source code
Scale security architecture reviews without scaling your security team.
Security reviews that satisfy auditors and keep engineering moving
Security reviews that satisfy auditors and keep engineering moving
PCI DSS, ISO 27001, and the EU Cyber Resilience Act now require formal threat modeling. SecurityReview.ai generates threat models directly from your architecture so compliance doesn’t depend on manual reviews.

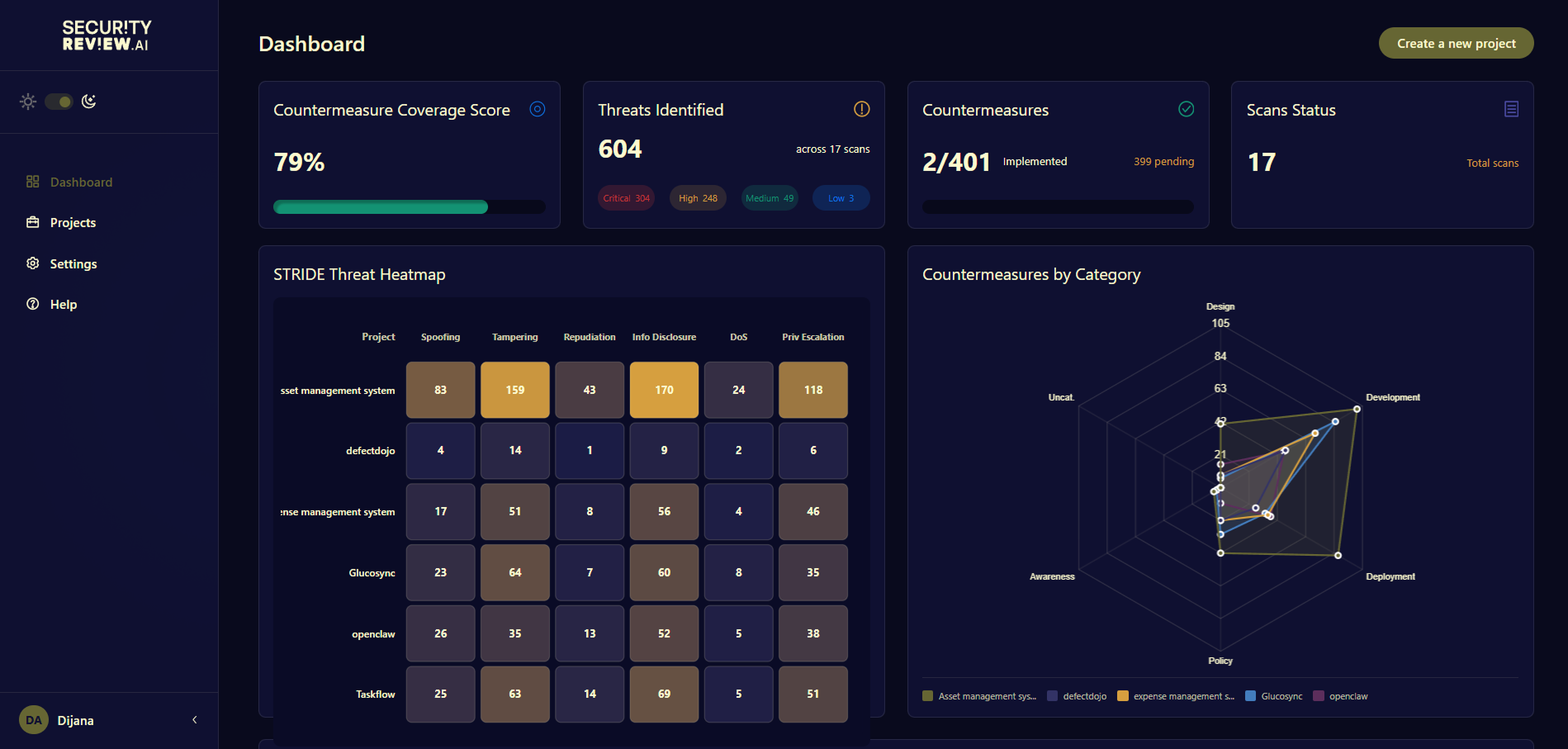
Catch design flaws before they become engineering problems
SecurityReview.ai analyzes your architecture and documentation to uncover security risks early, while the design is still evolving and fixes are simple.


Give developers security guidance
before the first line of code
Security risks are translated into clear and actionable requirements inside your development workflow, so teams know what to secure before implementation begins.

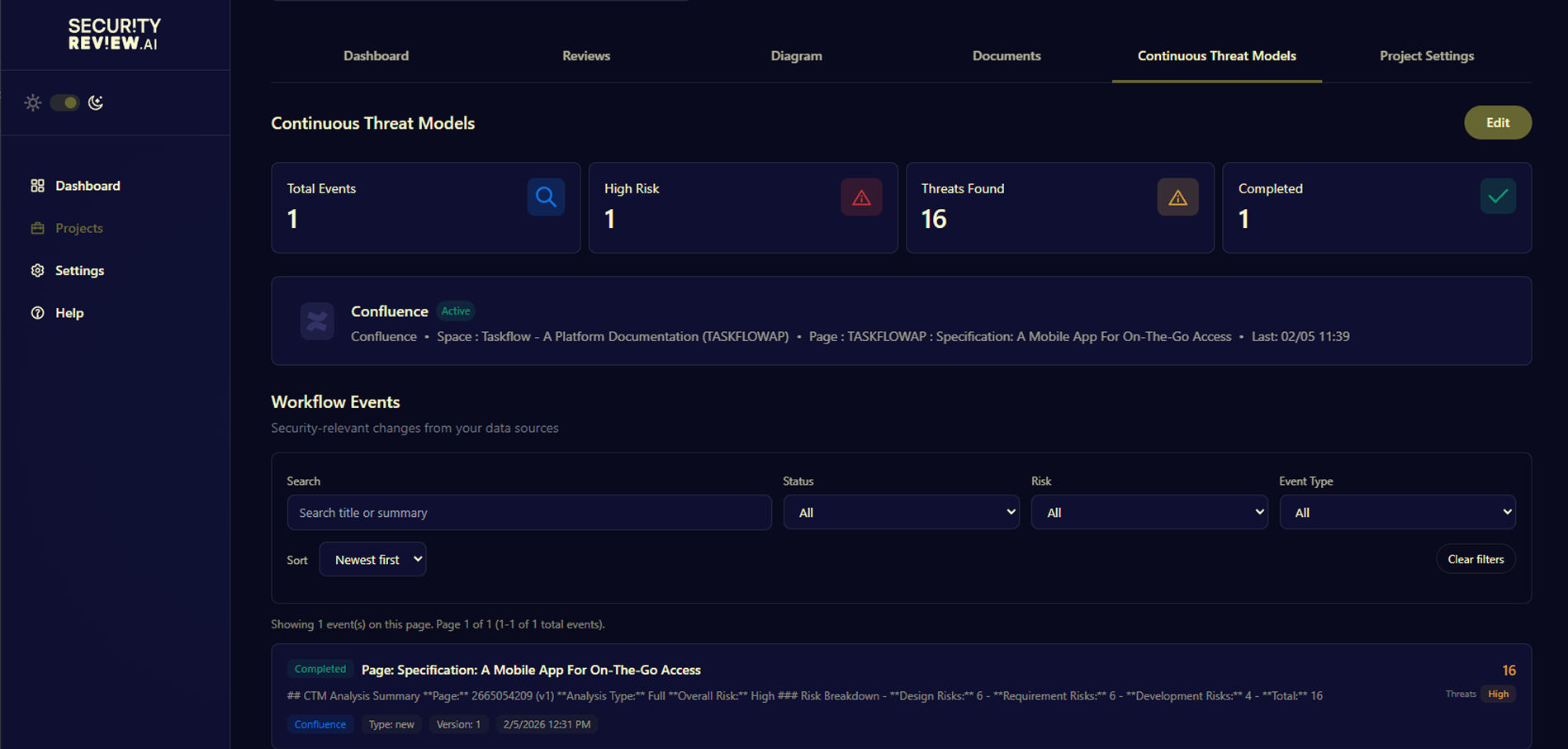
Keep your threat model in sync
with your system
As architecture, documentation, and code evolve, SecurityReview.ai continuously updates the threat model so security reviews never fall behind development.