Your Security Design Enforced in Every Line of AI-Generated Code
With security design and coding rules enforced during code generation, AI-generated code follows how your system is actually built

Works with your AI development stack






No Control Over Security in AI-Generated Code
AI coding tools make it easy to generate features quickly. The code looks clean, passes checks, and moves forward without friction.
But nothing in that process ensures it follows your security design or coding standards. Each feature gets generated differently, without enforced guardrails or consistent decisions.
Over time, access control, data flow, and trust boundaries start to drift, and risk builds quietly across the system.

Security That Doesn’t Stop at Design
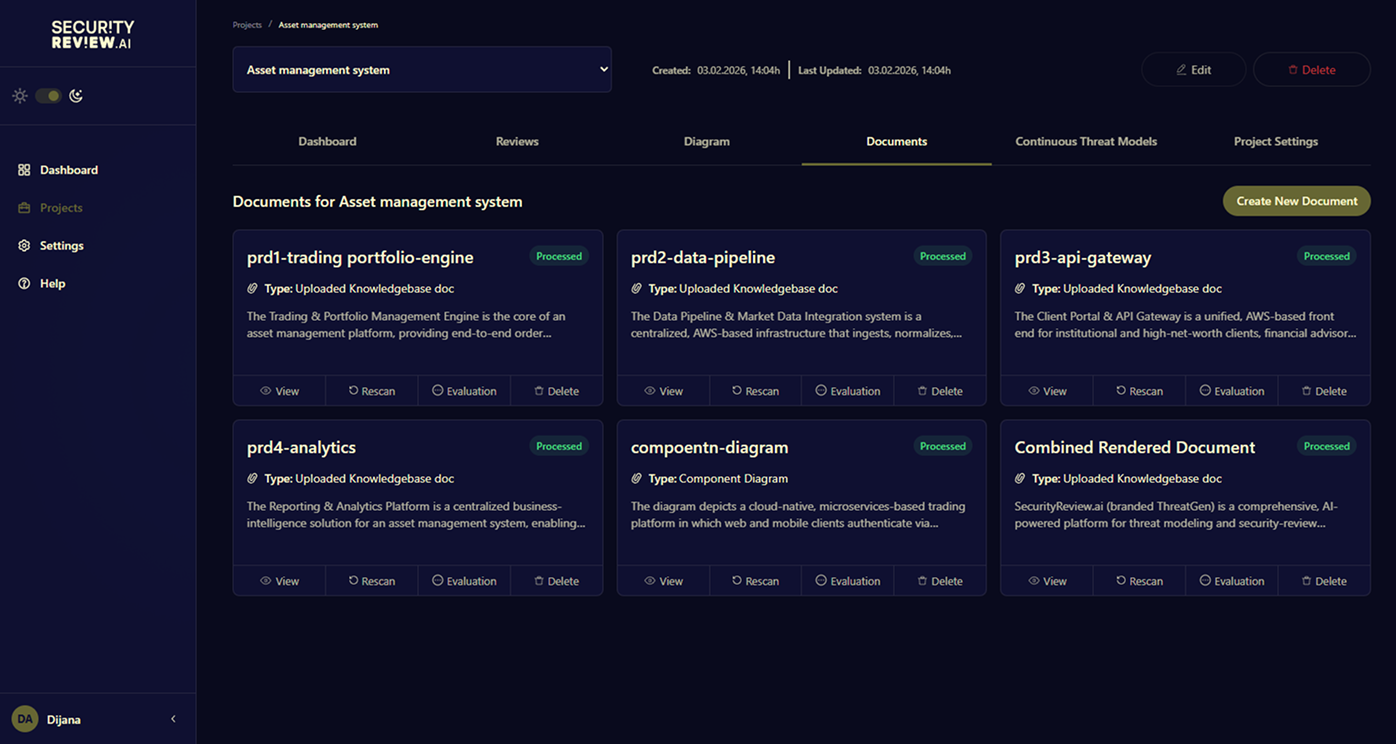
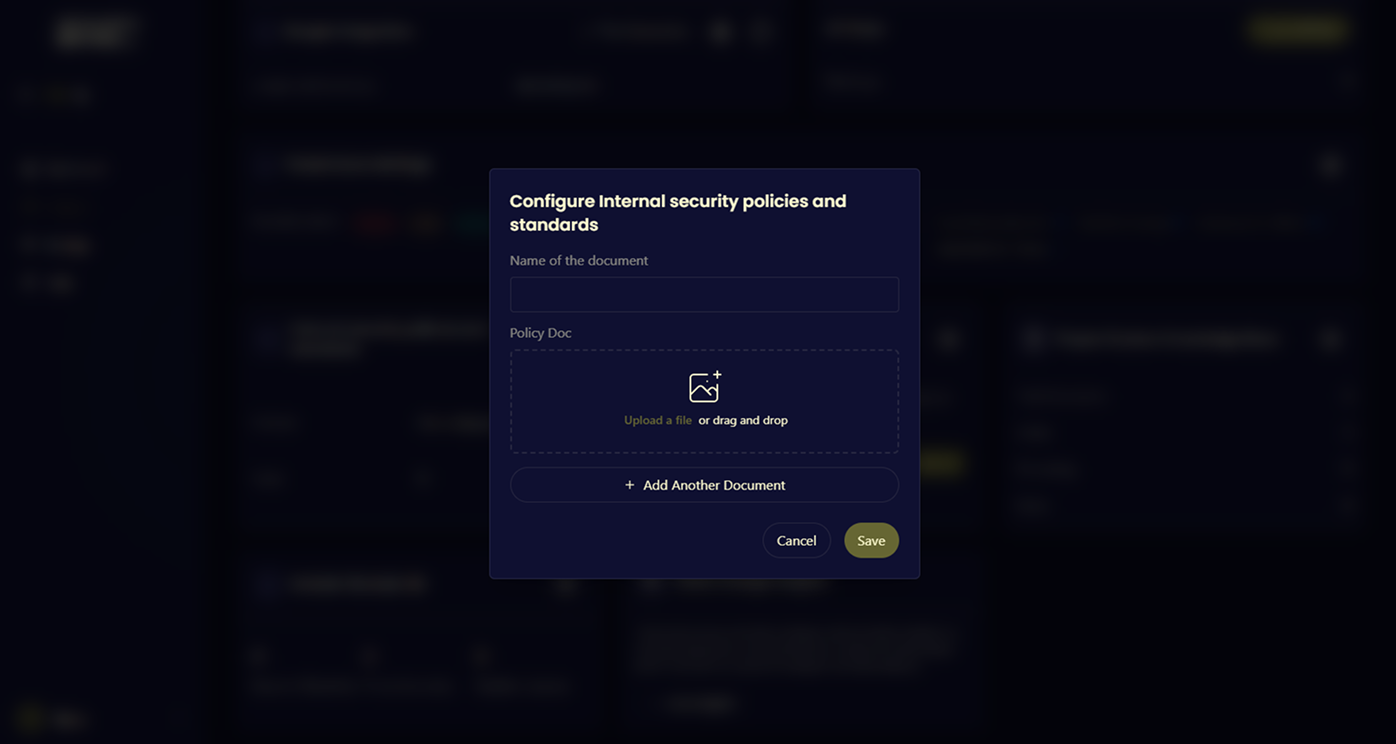
Understand your system
Analyze architecture, documentation, and engineering context to build an accurate model of how your system actually works.
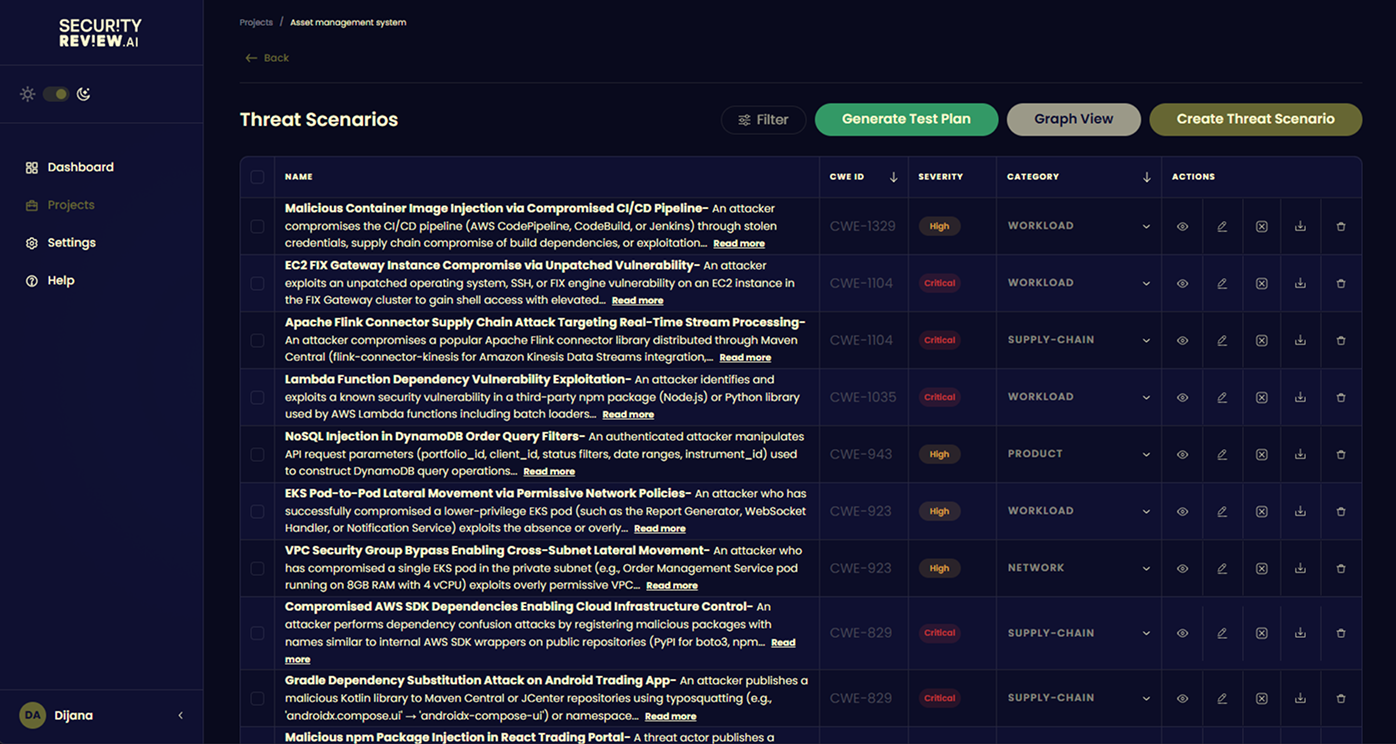
Define security design
Generate system-specific threat models, risks, and security decisions based on real services, data flows, and integrations.
Enforce during code generation
Apply security design and coding rules as code is generated, so every feature follows the same decisions from the start.
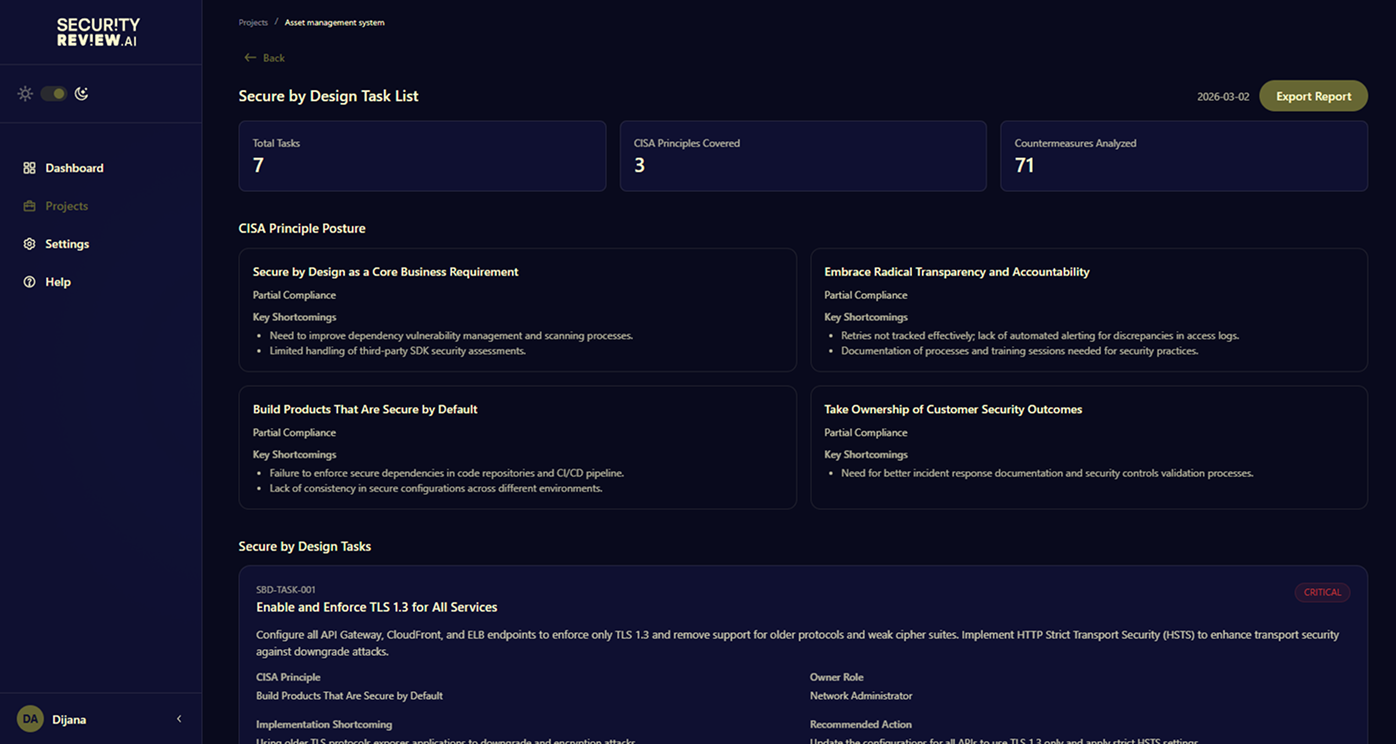
Generate audit-ready evidence
Map risks and decisions to compliance frameworks and maintain continuous, traceable security documentation.
Compliance Doesn’t Work Without Continuous Evidence
Mapped to: DORA • EU Cyber Resilience Act • PCI DSS • ISO 27001
Frameworks like DORA, PCI DSS, ISO 27001, and the EU Cyber Resilience Act require clear, traceable evidence of how security decisions are made and enforced.
SecurityReview.ai generates that evidence continuously by connecting your system design, risks, and controls, so compliance doesn’t depend on manual documentation or last-minute effort.
Security teams get continuous visibility into risk.
Auditors get provable and traceable controls.
Stop choosing between engineering velocity and regulatory readiness. Get both.