SecurityReview.ai: A Living Threat Model for Living Systems
Usually, threat models are created during a concentrated burst of attention: a design workshop, a sprint review, or a security checkpoint before release. The team maps trust boundaries, flags attack paths, and documents assumptions. It feels thorough and productive.
Then the system changes.
A Jira ticket quietly expands its scope after adding another integration, a pull request introduces a new library to meet a deadline, and a Confluence design gets edited after stakeholder feedback. None of these changes feels alarming on their own, but collectively, they change your attack surface.
Threat modeling, meanwhile, stays event-based. It captures a moment in time, while the architecture keeps moving.
And as more time passes by, it widens incrementally, change by change, until the documented assumptions no longer match production reality. By then, you’re making security decisions based on a version of the system that no longer exists.
Table of Contents
- No More Static Reviews
- Seeing Risk the Way Systems Actually Work with Continuous Threat Modeling
- Threat Modeling That Doesn’t Expire
No More Static Reviews
Keeping your products secure needs awareness of change.
In most organizations, meaningful changes to the system don’t automatically trigger meaningful updates to the threat model. But consider what actually shifts during a normal sprint:
- A Jira ticket expands in scope to support a new integration.
- A linked pull request modifies authentication logic.
- A design document updates a data flow to meet a business requirement.
Each of these changes can introduce new attack paths or reshape existing trust boundaries. Yet they rarely initiate structured security reconsideration.
The default response is heavy: schedule another review, reopen the document, gather the same stakeholders, reconstruct context from memory. But that approach doesn’t scale, so it often doesn’t happen.
When every Jira update has the potential to alter risk, and every linked PR can reshape how data moves through the system, threat modeling must respond to change automatically. Not through full rework, but through lightweight, contextual analysis triggered by what actually changed.
This isn’t always-on scanning that generates noise. It’s targeted review grounded in relationships across tools. It understands that:
- A design decision in Confluence connects to requirements in Jira.
- Those requirements connect to implementation in GitHub.
- A change in one node affects the others.
Threat modeling stops being a static artifact and starts behaving like what the system already is: a living structure that evolves incrementally. Security becomes aware of movement as it happens.
Seeing Risk the Way Systems Actually Work with Continuous Threat Modeling
Continuous Threat Modeling is built for the places where systems actually change: Jira tickets, Confluence pages, GitHub pull requests, and more. Instead of treating threat modeling as a one-time review, it treats it like monitoring with its lightweight analysis that runs whenever the underlying source changes.
Here’s the practical problem it solves. In a real sprint, the “design” isn’t just a Confluence page. It’s a chain:
- A Confluence page describes intent and architecture.
- Jira issues refine requirements, edge cases, and scope.
- GitHub PRs implement the reality (and introduce the surprises).
When those pieces shift independently, risk shifts too. The hard part isn’t finding a risk in one artifact, but in understanding how changes in one place ripple into the others.
That’s what Continuous Threat Modeling does differently. It follows the links.
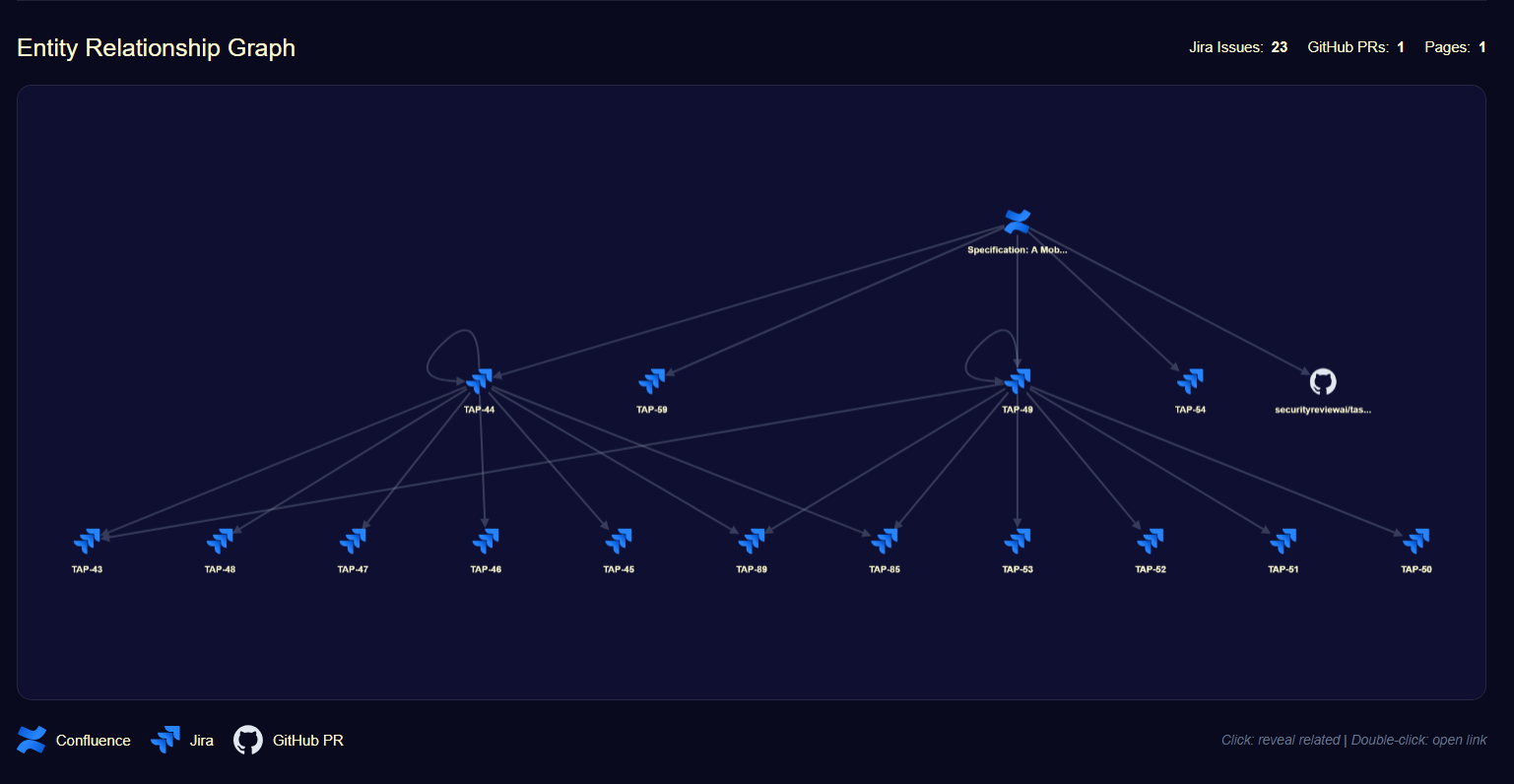
Instead of analyzing a single doc or ticket in isolation, it builds a connected view of the workstream and continuously evaluates deltas. You can see the structure as a tree of related items (pages, issues, PRs), which makes two things easier:
- You spot cascading impact (a requirement change that forces an auth change that alters trust boundaries).
- You trace risk origin based on where it entered the system:
- Design risks from Confluence (architecture, flows, trust boundaries)
- Requirement risks from Jira (scope changes, new integrations, data handling expectations)
- Development risks from GitHub (implementation details, dependency changes, auth logic, unsafe patterns)
This is a technical shift in how you reason about security: you stop reviewing artifacts as separate objects and start reviewing the relationships between them because that’s where attack paths form.
Threat Modeling That Doesn’t Expire
Threat modeling shouldn’t reset every sprint.
When your review process depends on scheduled workshops and manual checkpoints, it will always lag behind delivery. Continuous Threat Modeling changes that dynamic. It gives you:
- Continuous visibility without slowing delivery
- Feature-level awareness without adding headcount
- Risk traceability across design → requirement → code
- Security context embedded directly in engineering workflows
You stop reviewing snapshots and start monitoring movement. You stop reconstructing context and start seeing it in real time. And you stop guessing where risk originated because the system shows you.
If your architecture is alive, your threat model should be too.
Continuous Threat Modeling is now available inside SecurityReview.ai. Connect your Jira, Confluence, and GitHub projects, and let your threat model move with your system.
FAQ
Why does traditional threat modeling fail to keep up with system changes?
Traditional threat models are usually created during a single event, like a design workshop or a security checkpoint. They capture a moment in time, but the architecture keeps moving due to ongoing changes like Jira ticket scope expansions, new library introductions, and design edits. This gap causes the documented assumptions to no longer match production reality, leading to security decisions based on an outdated system version.
What is Continuous Threat Modeling?
Continuous Threat Modeling is an approach that treats threat modeling like a form of monitoring rather than a one-time review. It uses lightweight, contextual analysis that runs automatically whenever the underlying sources of change shift, such as Jira tickets, Confluence pages, and GitHub pull requests. It focuses on the relationships between these artifacts, not just the artifacts in isolation.
How is Continuous Threat Modeling different from static review processes?
Static reviews are heavy and don't scale. They require scheduling another meeting, reopening documents, gathering stakeholders, and reconstructing context, which often leads to them not happening. Continuous Threat Modeling automatically responds to change with targeted analysis, building a connected view of the workstream and continuously evaluating deltas across design, requirements, and code.
Where does Continuous Threat Modeling identify the origin of risks?
It traces risk origin based on where the change entered the system, specifically: Design risks from Confluence (architecture, flows, trust boundaries). Requirement risks from Jira (scope changes, new integrations, data handling expectations). Development risks from GitHub (implementation details, dependency changes, authentication logic, unsafe patterns).
What benefits does Continuous Threat Modeling provide to engineering teams?
This approach ensures that the threat model doesn't expire and keeps pace with delivery. It offers: Continuous visibility without slowing down the development process. Feature-level security awareness without needing additional headcount. Clear risk traceability across the entire workflow: design → requirement → code. Security context embedded directly within existing engineering workflows.
How can I implement Continuous Threat Modeling?
Continuous Threat Modeling is available within SecurityReview.ai. You can connect your existing Jira, Confluence, and GitHub projects to allow your threat model to evolve automatically alongside your system.















