SecurityReview.ai Launches Secure by Design Analysis Report

Secure by Design is mostly a performance that organizations say they follow. But only a few can prove that they do.
CISA didn’t publish Secure by Design so you could add a slide to your next leadership update. It set an expectation: security must be a core business requirement, built into how products are designed, shipped, and maintained. That expectation is now showing up in customer questionnaires, regulatory conversations, and executive risk discussions. Saying you're following Secure by Design no longer carries weight unless you can show how it manifests in your application, in specific controls, with named owners and measurable outcomes.
That’s exactly why we’re introducing the Secure by Design Analysis Report inside SecurityReview.ai.
Instead of treating Secure by Design as a declaration, the report evaluates how your application actually aligns with CISA principles, based on the countermeasures you’ve implemented and the evidence you provide.
Table of Contents
- From CISA Principles to Named Owners and Verifiable Tasks
- Make Secure by Design a Business Requirement
- See Exactly Where Your Application Stands
From CISA Principles to Named Owners and Verifiable Tasks
Teams read the CISA principles, agree they make sense, and then struggle to translate them into concrete actions inside a specific application.
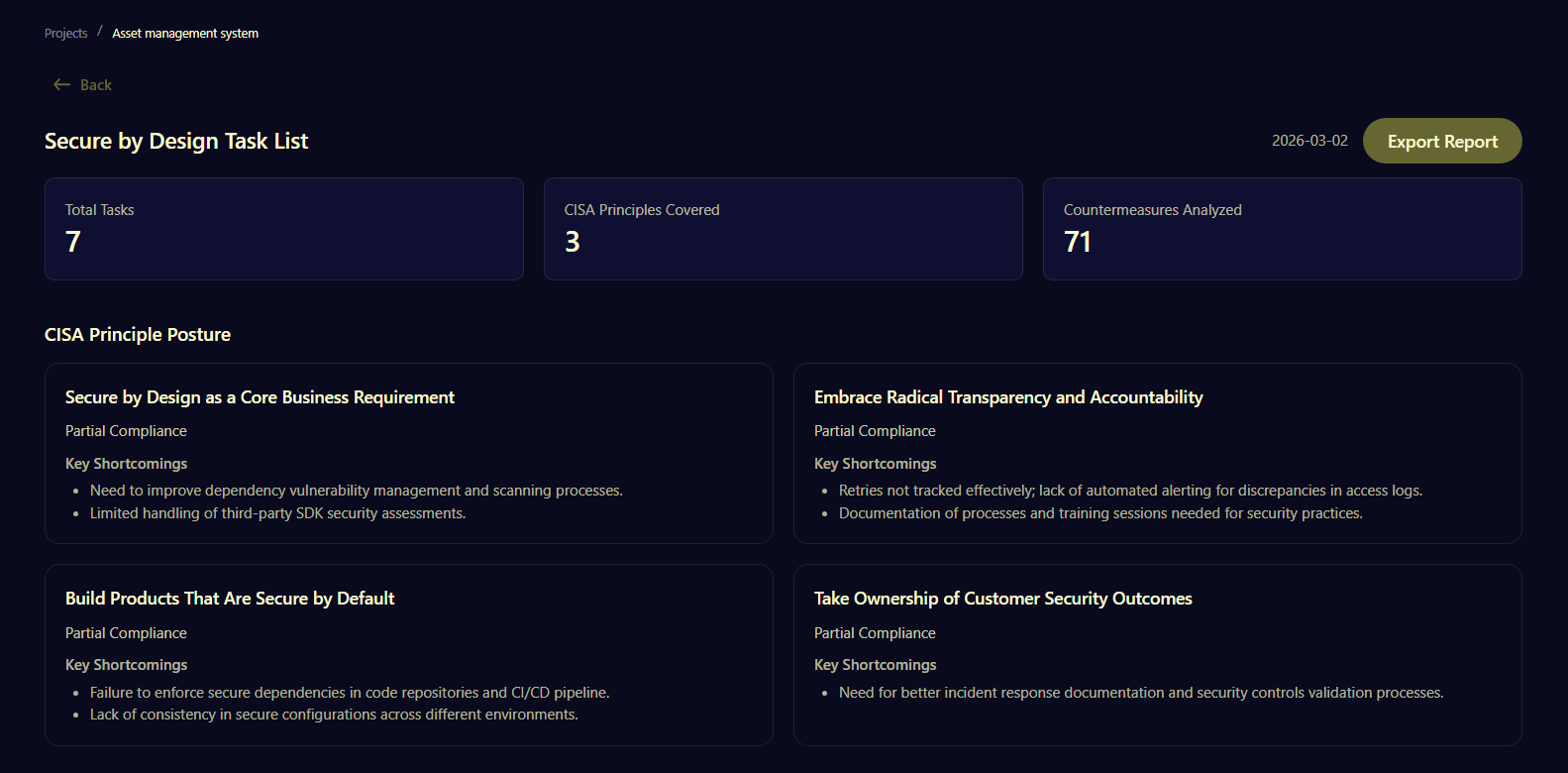
The Secure by Design Analysis Report closes that gap by starting with your actual system, not a generic checklist. It analyzes implemented countermeasures, reviews the evidence you provide, and evaluates how those controls align with each CISA principle. The outcome is a structured application-specific task list.
At a high level, the report does three things:
- Assesses your posture against each core CISA Secure by Design principle
- Identifies key shortcomings based on real implementation evidence
- Generates tailored tasks tied directly to those shortcomings
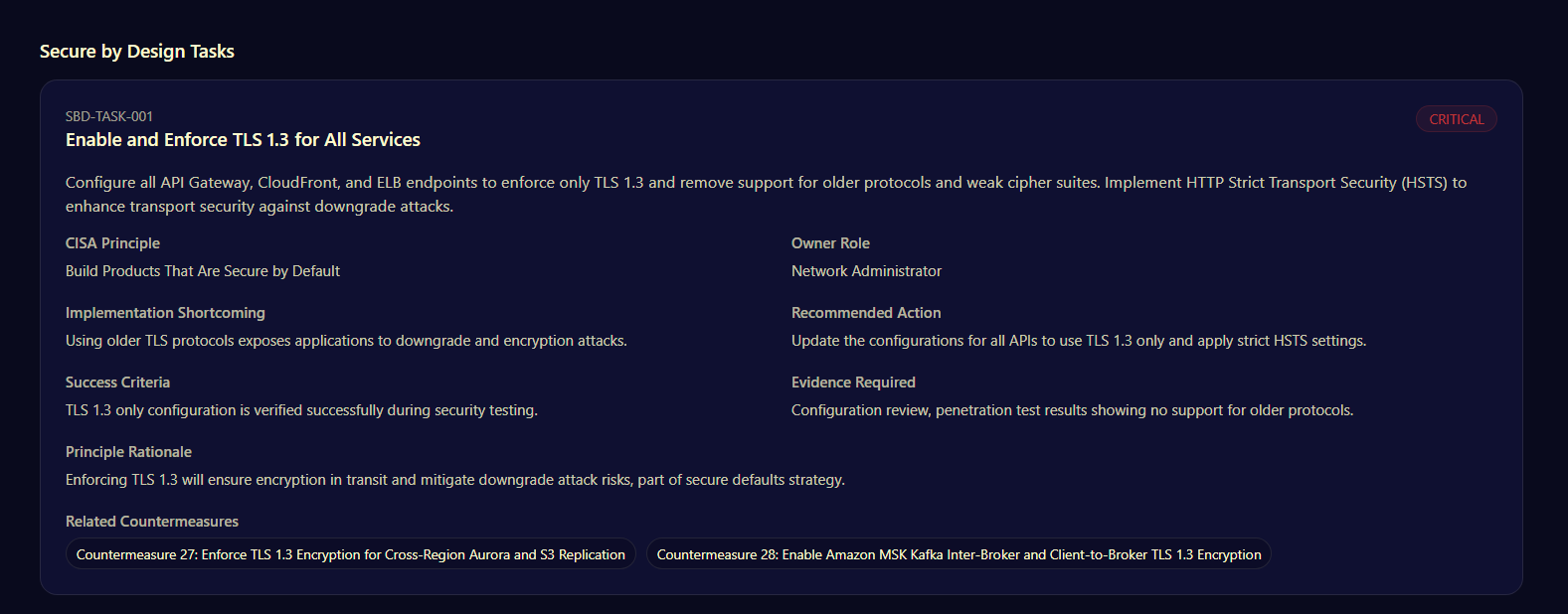
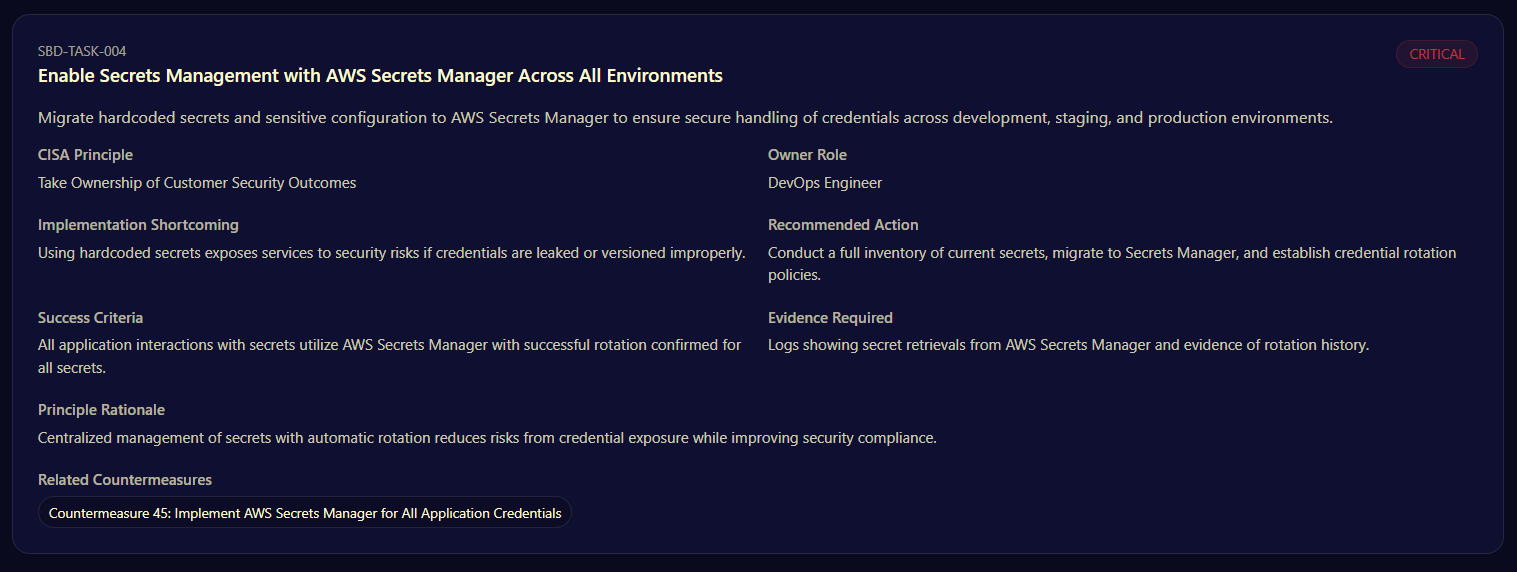
Each generated task is not a vague recommendation. It includes:
- The specific CISA principle it supports
- The responsible role expected to act
- The implementation shortcoming it addresses
- A recommended action grounded in your environment
- Clear success criteria and required evidence
That structure forces alignment between policy and execution. If a principle like “Build Products That Are Secure by Default” shows partial compliance, you don’t just see the label. You see where secure defaults break down in practice and who is accountable for fixing it.
Instead of debating whether you are aligned with CISA, you get a concrete view of where alignment holds and where it doesn’t. And because every task is tied to a principle and supported by evidence requirements, remediation becomes traceable rather than informal.
Secure by Design becomes a set of assigned responsibilities, backed by verifiable outcomes.
Make Secure by Design a Business Requirement
If engineering sees Secure by Design as an extra process, if product sees it as a compliance exercise, or if leadership sees it as a quarterly update item, then it never becomes what CISA intended: a core business requirement that shapes how software is built and operated.
The Secure by Design Analysis Report surfaces where that disconnect exists inside your application.
When the report identifies partial compliance across principles, it doesn’t just point to technical gaps. It exposes operational friction:
- Dependency risks that are not consistently enforced in CI/CD
- IAM policies that drift beyond least privilege
- Logging that exists but does not support accountability
- Training expectations that are defined but not validated
These are signs that Secure by Design has not been fully embedded into engineering ownership and delivery standards.
This is important especially for leadership. Because when Secure by Design is treated as a business requirement, it changes how decisions get made. It influences release criteria. It shapes architectural reviews. It assigns responsibility before incidents occur, not after.
With a structured, principle-aligned task list, leadership gains something they rarely have: a defensible line of sight from high-level Secure by Design commitments down to specific roles and required actions inside the application.
You can answer questions that usually create hesitation:
- Where are we misaligned with CISA principles?
- Who is accountable for closing those gaps?
- What evidence shows that we followed through?
This is how Secure by Design becomes measurable. Not as a slogan, but as an operating standard that engineering teams can execute and leadership can validate.
See Exactly Where Your Application Stands
Secure by Design only works when it’s visible, owned, and enforced inside the product itself. Principles alone don’t reduce risk. Assigned tasks, verified controls, and accountable roles do.
With the Secure by Design Analysis Report in SecurityReview.ai, you see exactly where your application stands against CISA principles and what needs to change next. No generic checklists. No abstract scoring. Just application-specific gaps, named owners, and verifiable actions that turn intent into execution.
If Secure by Design is going to be a business requirement in your organization, make it operational. Generate your Secure by Design Analysis Report inside SecurityReview.ai, and replace declarations with documented proof.
FAQ
What is the Secure by Design Analysis Report?
It is a feature inside SecurityReview.ai designed to evaluate how an application aligns with CISA's Secure by Design principles. Instead of a simple declaration, it analyzes implemented countermeasures and evidence to provide a concrete, application-specific assessment.
How does the Secure by Design Analysis Report turn CISA principles into action?
The report translates abstract CISA principles into a structured, application-specific task list. It starts with your actual system to assess alignment, identify key shortcomings based on real implementation evidence, and then generates tailored, concrete tasks to address them.
What specific details are included in each task generated by the report?
Each task is highly specific and includes: The specific CISA principle it supports. The responsible role expected to act (named owners). The implementation shortcoming it addresses. A recommended action grounded in your environment. Clear success criteria and required evidence for completion.
What is the core difference between a "Secure by Design" declaration and the Analysis Report?
A declaration is simply saying you follow the principles, which carries less weight. The Analysis Report provides documented proof. It replaces informal discussions with a concrete view of where alignment holds and where it doesn't, making remediation traceable and verifiable.
How does the report help leadership make "Secure by Design" a business requirement?
It gives leadership a clear, defensible line of sight from high-level Secure by Design commitments down to specific roles and required actions inside the application. By exposing partial compliance, it points out operational friction like drifting IAM policies or unvalidated training, which are signs that security is not fully embedded as a core business standard.
What key questions can the Secure by Design Analysis Report answer for an organization?
The report provides clear answers to critical questions that often cause hesitation, such as: Where are we misaligned with CISA principles? Who is accountable for closing those gaps? What evidence shows that we followed through?
Is the report based on generic checklists or abstract scoring?
No. The Secure by Design Analysis Report provides application-specific gaps, named owners, and verifiable actions. It avoids generic checklists and abstract scoring to focus on making Secure by Design operational and measurable within your product.















